A friend of mine was hacked this year. I received two Facebook notifications from them:
- A DM in textbook phishing format, with strange URL link (showing https I might add) and an accompanying “is this your picture? xx.😨”
- A notification that I was tagged along with 58 others in a photo.
I screenshot the message and sent it to them on another app immediately.
“What should I do now?”
Changing the account password (or attempting to) is always the obvious first step. I confirmed that she’d done this.
“Change all your email passwords. Consider also changing passwords for all your major accounts (like finance, health, investments) too. Did you turn 2FA on?”
“What is 2FA?”
“It’s an additional layer of security for your account login process. There’s different kinds but in general, pick an app authenticator and avoid any SMS options whenever possible.”
“Okay, so what should I use? I might try Duo.”
“Yeah Duo is good. Microsoft, Google and Okta are also good options.”
(On a side note, it’s important to mention that -while a sound password manager- Authy requires your phone number for registration.)
“Should I start using a password manager?”
“Definitely. I’d recommend using BitWarden.“
“I’ve heard about LastPass and other ones, are they not as good?”
“I used to use LastPass, until they added the restriction for free accounts to only one device. It words fine, I just didn’t want to start paying for something I didn’t need to. BitWarden was recommended as an alternative, and it’s basically the same.”
“But are the different features worth looking into at all?”
“Maybe later. The important thing right now is that you start using a password manager now.”
What a Password Manager is (and isn’t)
Let’s be clear about one thing: a password manager is not a solution, it is a tool in the shed.
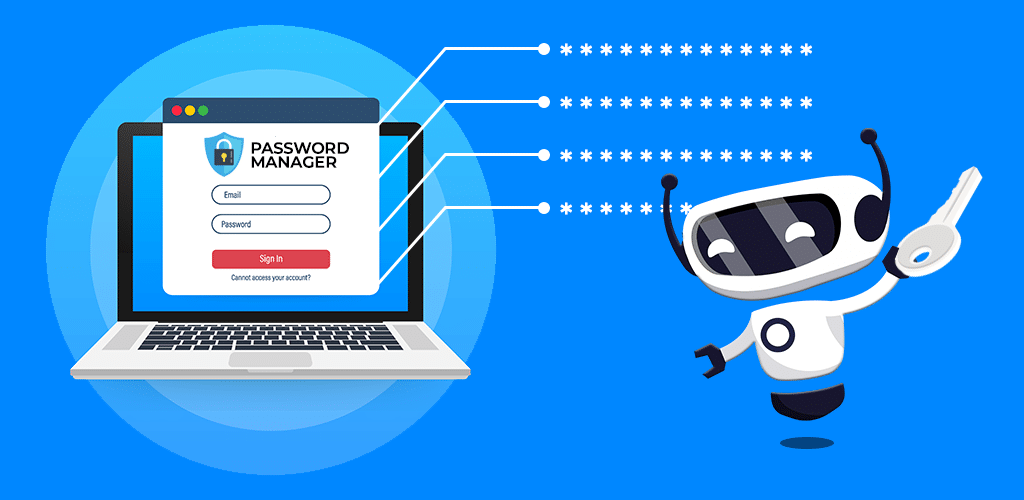
It’s a virtual self defense tool – one of many at your disposal. It has a simple purpose: to serve as your single point of control for all passwords.
Registration is standard: enter new account details and a password. This password can be changed, but it cannot be reset. If you lose this password, you lose the account, and all the passwords in it.
Convenience
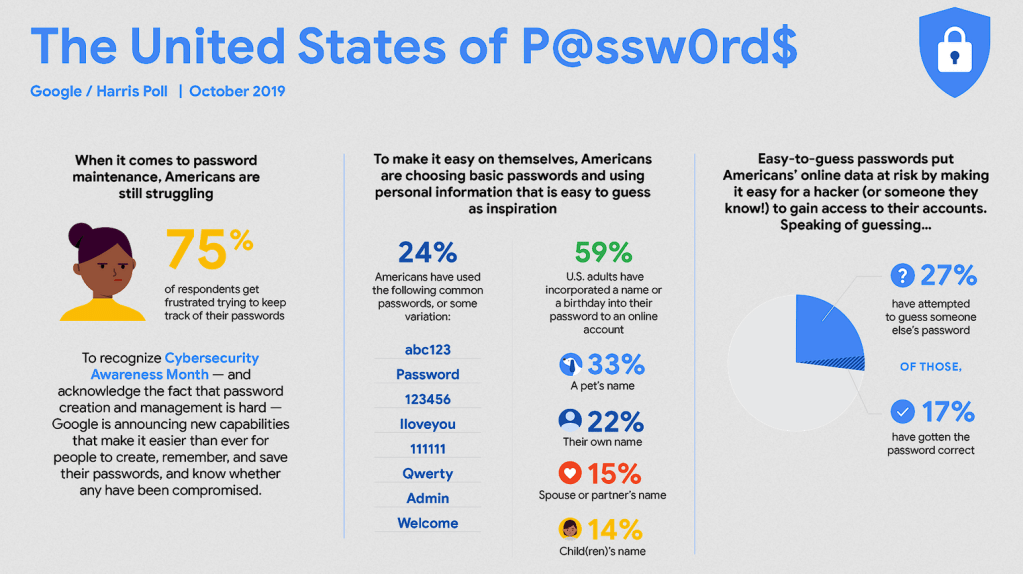
Not all of us have good password habits. Hackers using data dictionaries (databases of common passwords) that are decades old to this day for a reason: it works.
The reason why it works is passwords can be a pain. We wouldn’t seek shortcuts if the convenience wasn’t such a relief. But with literal notebooks sold as “password managers”, the situation is dire indeed (still better than holding a sheet of passwords in your wallet).
Reused passwords are very common. One account compromised can quickly snowball into multiple accounts and possibly banking, email or private cloud storage also being accessed.
Password Managers can be accessed via phone app or browser plugin, and it really is a whole world of difference when it comes to convenience.
There’s no longer a need to enter nearly as many passwords manually. Updating passwords is easy, with options like character types to include (numbers, symbols, letters) and customisable length.
Biometric authentication is truly the one feature that makes using a Password Manager fast and seamless.
At A Cost
By the same token, enabling biometrics also opens you up to associated risks.
Worst case scenario: someone unlocks your phone using biometric access – if your Password Manager access is also linked to biometrics, that’s game over. Just a fingerprint – that could be all that’s needed to access to everything in your private life.

Of course, it can be even easier to bypass biometrics without you being conscious or consenting. In some cases, we’ve also seen taped-up glasses being used on sleeping victims to bypass iPhone biometric authentication.
Risk Prevention
A potentially effective counter would be to use applocking on your most important/private phone apps – adding either a PIN, pattern or biometric authentication for two layers of security. I’ve personally used AppLock on Android but here are other options to consider. Just keep in mind for the free offerings you’ll be introduced to ads.
This roughly equates to double locking a door. It’s more time consuming to open, but it boils down to whether you believe the added layer of security is worth it.

Another added risk is if you use the add-on on an open browser, you must lock your computer each time you walk away.
A great alternative authentication method is using a YubiKey for 2FA. There are many types of YubiKeys, but they are all physical security products that can provide access not only to a Password Manager but also phones, computers, or networks that you may own. They range between around $40 to over $110.
Why BitWarden?
I’ve saved passwords to my Google account before, and I’ve also used the built-in ones for browsers. I used LastPass for a few years until they made the change to free plans – restricting the use of their software on one device only.
Since then I’ve made the switch to BitWarden, a no-frills open-source and free password manager. As a free user I’ve had no complaints – it’s minimal, simple and I’ve never run into any technical difficulties.
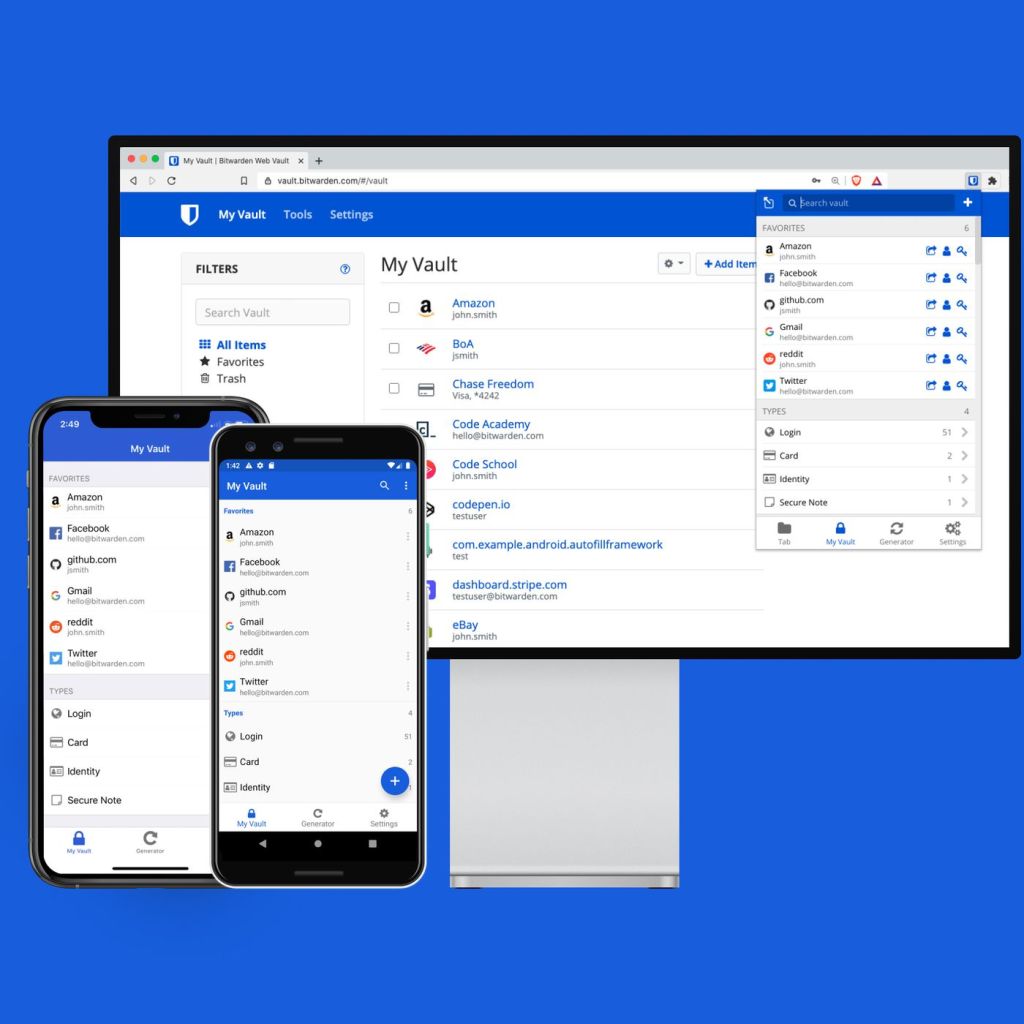
Password storage is unlimited – and multi-sync works across most operating systems and browsers. Their paid offering is inexpensive at $10USD and includes pretty big features: multi-factor authentication options (YubiKey, FIDO2, Duo), Bitwarden Authenticator (TOTP) and “emergency access” you can provide to a trusted friend or family. Other nice extras include 1GB cloud storage and Vault Health Reports which crosscheck your vault with exposed passwords from known data breaches.
Some of the cons I’ve seen talked about are: no live chat/phone support, business plan needed for sharing passwords with 5+ users, and a lack of custom categories. Posts about app crashes are numbered, in my experience it’s always been fast and reliable.
The no-frills approach really simplifies the experience of using it, and is accessible to anyone using a password manager for the first time.
Open Source – a big deal?
The number of open-source password managers is very short indeed. So why is being open source such a big deal, and what does it mean when other market contenders aren’t?
BitWarden is completely open-source (GitHub). Being open source means that the software is transparent: all its inner workings are publicly accessible.
This is particularly important with password managers, because we’ve seen multiple instances of major password manager apps with vulnerability after vulnerability reported on a regular basis: stand-out examples from 2016, 2017, 2019 and 2021.
With BitWarden’s source code open source, this means that security vulnerabilities and bugs are reported by the programming community at a rate much faster than say, reading an advance copy of a soon-to-be-published security vulnerability report.

